Table of contents
- Key Takeaways
- Introduction
- How does Entra ID Governance work?
- What do lifecycle workflows automate?
- How does entitlement management reduce access request tickets?
- What happens during an access review?
- How does Privileged Identity Management protect admin accounts?
- What licenses does Entra ID Governance require?
- How do MSPs implement Entra ID Governance?
- Connecting identity governance to the management platform
- Stop provisioning accounts manually
- Frequently Asked Questions About Entra ID Governance
Key Takeaways
- Microsoft Entra ID Governance automates the full identity lifecycle: provisioning new users, adjusting permissions when roles change, and revoking access the moment someone leaves.
- MSPs use it to eliminate per-tenant manual onboarding and offboarding, replacing ticket-driven workflows with policy-driven automation across all client environments.
- Four components work together: lifecycle workflows, entitlement management, access reviews, and Privileged Identity Management (PIM).
- HR system integrations with Workday and SAP SuccessFactors trigger identity actions automatically, so accounts are ready before day one and disabled before the offboarding email goes out.
- Licensing is separate from standard Microsoft 365 plans. Factor Entra ID P2 or Governance costs into client proposals when recommending identity governance improvements.
Introduction
Microsoft Entra ID Governance solves a problem every MSP knows too well: user access that’s either too slow to provision or too slow to revoke. New hires wait days for accounts. Departing employees keep access for weeks. Role changes sit in ticket queues while permissions drift out of alignment with actual job functions.
The platform turns identity management into a policy-driven, automated process. Administrators define who should have access to what based on job attributes, organizational rules, and time limits. Entra ID Governance enforces those policies across Microsoft 365, Azure, and connected SaaS applications without requiring manual intervention for every change.
For MSPs managing multi-tenant environments, Entra ID Governance means defining access policies once and applying them consistently across the entire client base. Administrators stop logging into individual tenants to provision accounts or track down stale permissions.
How does Entra ID Governance work?
Microsoft Entra ID Governance runs on four integrated components that share a common policy engine and audit log, giving MSPs a single framework for managing identity risk across every client tenant.
Entra ID Governance runs on four components that share a common policy engine and audit log. Lifecycle workflows handle joiner/mover/leaver processes, automating account creation when someone starts, permission changes when they switch roles, and access removal when they leave. Entitlement management turns access requests into self-service with approval routing and automatic expiration. Access reviews run recurring certification campaigns so reviewers periodically confirm existing permissions are still appropriate. And Privileged Identity Management controls admin access through just-in-time elevation instead of standing privileges.
The integration between these pieces matters. An access review can flag permissions that were granted through entitlement management. A lifecycle workflow can trigger when PIM detects an admin role that’s been inactive. The audit log captures everything in one place rather than scattering events across separate systems.
According to Microsoft’s official Entra ID Governance documentation, the platform is designed to balance the need for security and employee productivity with the right processes and visibility.
What do lifecycle workflows automate?
Lifecycle workflows eliminate the provisioning ticket entirely. When HR data changes, identity actions execute automatically, without anyone submitting a request.
Lifecycle workflows handle the account provisioning and deprovisioning tasks that eat up technician time. They execute automatically based on signals from connected HR systems or scheduled triggers.
- Onboarding automation: When an employee record appears in Workday or SAP SuccessFactors with a future start date, lifecycle workflows can pre-create the Entra ID account, assign group memberships based on department and location, provision access to required applications, and send the new hire a welcome email with a temporary access pass. All of this happens before day one without anyone submitting a ticket.
- Offboarding automation: When HR marks someone as terminated, workflows revoke refresh tokens within minutes, remove access package assignments, disable the account, and preserve mailbox data according to retention policies. The three-month gap between someone leaving and IT finally disabling their account disappears.
- Role change handling: Job title or department changes in the HR system trigger workflows that add new group memberships, remove outdated ones, and adjust application access accordingly. The employee’s permissions stay aligned with their actual responsibilities.
How does entitlement management reduce access request tickets?
Entitlement management replaces the IT ticket queue with a self-service portal. Business managers approve access requests for their own teams, and governance controls stay intact without routing everything through IT.
Entitlement management bundles related resources into access packages that employees can request through a self-service portal called My Access. Instead of submitting separate requests for a SharePoint site, a Teams channel, and an application role, users request a single package that includes everything they need for a specific function.
Each package combines resource assignments (groups, app roles, SharePoint sites), approval policies that route requests to the right people, time limits that automatically expire access after 90 days or six months, and renewal options for extending access before it lapses. The configuration happens once per package type, not once per request.
Business managers approve access requests for their teams instead of routing everything through IT. Governance controls and audit trails remain intact while shifting approval decisions to the people who actually understand whether the request makes sense.
Guest access for contractors and partner organizations works through the same system. External users request access, approvers sign off, Entra ID creates the B2B guest account automatically, and access expires when the engagement ends.
What happens during an access review?
Access reviews force periodic recertification of every permission, giving reviewers the context they need to make real decisions rather than rubber-stamping approvals.
Access reviews force periodic recertification of existing permissions. Administrators configure review campaigns targeting specific groups, applications, or admin roles, and designated reviewers receive tasks to confirm whether each person still needs their current access.
Microsoft added decision context that makes reviews more than checkbox exercises. Reviewers now see when the user last signed in, their recent activity in the application under review, how long they’ve held the access, and whether similar users have the same permissions. That last one matters: if everyone else in the same role has this access and the user is actively using it, the approval decision is obvious. If nobody in that role has this access except one person who hasn’t logged in for six months, so is the denial.
Reviewers can approve, deny, or mark “don’t know” for each assignment. Denied access gets removed automatically. The Access Review Agent in Microsoft Security Copilot can summarize reviewer workloads and suggest decisions based on activity patterns, though humans make the final call.
For compliance purposes, every review decision gets logged with timestamps, reviewer identity, and justification. When auditors ask how access verification works, the documentation already exists.
How does Privileged Identity Management protect admin accounts?
PIM eliminates standing admin access across all managed tenants. Attackers who compromise a credential get an account with no active permissions, not the keys to the entire environment.
Privileged Identity Management removes standing administrative access. Instead of users holding permanent Global Admin or Exchange Administrator rights, they hold eligible assignments that require activation when needed.
When someone needs admin access, they request elevation to a specific role with a justification and expected duration. The request can route through an approval workflow if configured. MFA confirms identity. Then the role activates for a set period, typically one to eight hours, and expires automatically when that window closes. No manual deactivation required.
A compromised account with an eligible PIM assignment can’t access admin functions without going through that activation sequence. Attackers would need to complete MFA, provide justification, and potentially get approval from another person.
PIM also runs its own access reviews specifically for privileged roles. Admin access gets recertified on a regular schedule separate from general permission reviews.
What licenses does Entra ID Governance require?
Entra ID Governance capabilities are not included in Business Premium or E3. Build license costs into every governance proposal or the project economics fall apart.
Entra ID Governance capabilities require licensing beyond standard Microsoft 365 subscriptions. The specific requirements depend on which features the deployment needs:
| Feature | License requirement |
|---|---|
| Lifecycle workflows | Microsoft Entra ID Governance or Entra Suite |
| Entitlement management (basic) | Microsoft Entra ID P2 |
| Entitlement management (full) | Microsoft Entra ID Governance |
| Access reviews | Microsoft Entra ID P2 or Governance |
| Privileged Identity Management | Microsoft Entra ID P2 |
Licenses apply to governed users, not administrators. Managing access reviews for 500 users means those 500 users need appropriate licensing.
For MSPs, licensing affects service pricing. Governance features aren’t included in Business Premium or E3 plans. Factor license costs into proposals when recommending identity governance improvements to clients.
How do MSPs implement Entra ID Governance?
Most successful deployments start with PIM. It delivers immediate risk reduction, requires no HR integration, and builds the internal governance habit before tackling more complex workflows.
Deploying everything at once rarely works. Most implementations start with the capability that addresses the biggest current pain point.
- PIM is usually the quickest win. Removing standing admin access takes minimal configuration and immediately reduces privileged access exposure across managed tenants. No HR system integrations required, no workflow design, just activation policies and MFA requirements.
- Access reviews make sense once PIM is running. Start with applications where inappropriate access creates actual risk: financial systems, HR platforms, and admin portals. Quarterly campaigns build the recertification habit without overwhelming reviewers. Expanding to broader application access can wait until the process is proven.
- Lifecycle workflows need an HR connection. Without data flowing from Workday, SuccessFactors, or another HR system, lifecycle workflows have nothing to trigger against. Pick a client organization that already has a supported HR platform integrated with Entra ID. Automate onboarding first, measure the reduction in provisioning tickets, then tackle offboarding and role changes.
- Entitlement management comes last for most MSPs. It requires the most upfront design work: defining access packages, mapping approval chains, training business managers on the My Access portal. Self-service access requests reduce ticket volume significantly, but the earlier components need to be stable first.
Connecting identity governance to the management platform
Identity governance only closes the loop when it’s connected to ticketing, billing, and monitoring. Separate logins for every tenant mean manual reconciliation, missed alerts, and margin leak.
Standalone governance tools create extra work. Separate logins for each tenant. Manual exports to reconcile license counts against billing. Security alerts that live in the Entra portal, while tickets live somewhere else. The access review was completed last Tuesday, but the technician handling the related ticket has no idea.
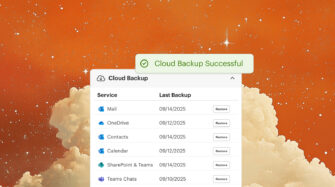
When the Microsoft 365 management platform connects directly to Entra ID, user changes sync automatically into ticketing, billing, and security monitoring workflows. A license addition in Entra ID updates billing records without manual reconciliation. A terminated user triggers alerts in the monitoring dashboard.
Security baseline monitoring catches configuration drift that could undermine governance policies. If someone disables MFA requirements or modifies conditional access rules, the alert fires before the next access review.
Cloud backup for Entra ID protects the identity infrastructure itself. A misconfigured lifecycle workflow or accidental bulk deletion becomes recoverable instead of catastrophic.
Stop provisioning accounts manually
Every hour technicians spend creating user accounts, resetting passwords, or chasing down stale permissions is an hour not spent on billable work. Multiply that across dozens of tenants and the labor cost eats into margins.
Syncro connects directly to Microsoft Entra ID across all client tenants from a single dashboard. Password resets and MFA enforcement take two clicks instead of portal hopping. License changes sync to billing automatically. Security baselines catch configuration drift before it becomes a compliance finding. And cloud backup means a misconfigured policy or accidental deletion doesn’t turn into a disaster.
Clients expect their MSP to have identity governance figured out. The next auditor who asks about access controls shouldn’t send the team scrambling.
Start a free trial and put identity management inside the same platform that runs everything else.
Frequently Asked Questions About Entra ID Governance
Microsoft Entra ID Governance is an identity management platform that automates user provisioning, access certification, and privileged account management across Microsoft 365 and Azure environments. It connects to HR systems to trigger identity lifecycle actions automatically and provides audit-ready documentation for compliance purposes.
Entra ID P2 includes access reviews and PIM. Entra ID Governance is a separate, higher-tier license that adds lifecycle workflows and the full version of entitlement management. Organizations that need to automate joiner/mover/leaver processes with HR system integration require the Governance license, not just P2.
The core governance features (lifecycle workflows, access reviews, entitlement management, PIM) operate within a single tenant. MSPs managing multiple client tenants need to configure governance policies per tenant. A unified management platform like Syncro can connect to all tenants from a single dashboard to streamline administration, monitoring, and billing across the client base.
Entra ID Governance integrates natively with Workday and SAP SuccessFactors for HR-driven provisioning. Integration with other HR systems is possible through the SCIM provisioning framework. When an employee record changes in the connected HR system, lifecycle workflows execute automatically based on those signals.
PIM can typically be configured in a single sprint for a single tenant. Access reviews take slightly longer because they require defining scope, identifying reviewers, and establishing a recertification cadence. Lifecycle workflows are the most time-intensive, because they require a working HR integration before anything can trigger. Most MSPs phase implementation over 60 to 90 days, starting with PIM and building from there.
Denied access is removed automatically at the close of the review cycle. The removal is logged with the reviewer’s identity, the decision, and a timestamp. No manual follow-up from IT is required. This automatic enforcement is what makes access reviews operationally viable at scale.
PIM eliminates standing administrative access. Instead of holding permanent Global Admin or other privileged role assignments, users hold eligible assignments that require activation on demand. An attacker who compromises a credential gains an account with no active admin rights. They would need to complete MFA, provide justification, and potentially receive approval from a second person before any privileged access is granted, making credential-based attacks significantly harder to execute.
Every governance action, including provisioning events, access review decisions, PIM activations, and entitlement management approvals, is logged in the Entra ID audit log with timestamps, actor identity, and justification. For compliance reviews, the documentation already exists and can be exported without requiring IT teams to reconstruct events manually.
Share